TL;DR
- DPRK-linked groups stole $2.06 billion in crypto during 2025.
- The Bybit exploit alone resulted in roughly $1.5 billion in losses.
- Hackers converted 86% of Bybit’s stolen ETH into Bitcoin within one month.
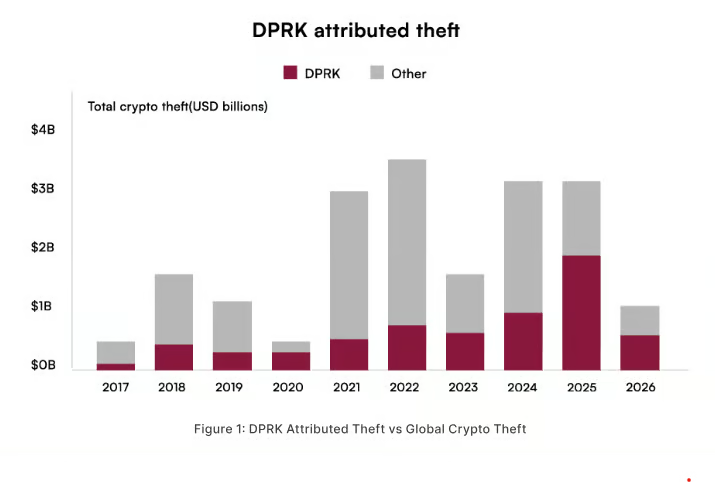
North Korean-linked cyber groups stole $2.06 billion in cryptocurrency during 2025, capturing roughly 60 percent of all value lost to hacks across the digital asset space, according to a new CertiK Skynet report.
The same report documents a total of $3.4 billion in crypto security losses over 656 incidents last year, attributing 79 of those events to operatives tied to the Democratic People’s Republic of Korea (DPRK). The data signals a clear departure from scattered intrusions toward a concentrated, state-level extraction model that directly funds Pyongyang’s nuclear and ballistic missile programs.
CertiK’s analysis, which includes onchain research from independent investigator Taylor Monahan, calculates that DPRK-linked actors accumulated $6.75 billion in stolen cryptocurrency between 2016 and early 2026 across 263 documented incidents. The figures transform what many once viewed as a cybersecurity nuisance into a core state revenue mechanism.
Open-source intelligence assessments confirm that hard currency from these thefts flows into weapons development, elevating digital asset crime from a financial integrity problem into a matter of international security. United Nations monitors and US intelligence agencies have repeatedly drawn the same line between crypto heists and missile launches.
The 2025 incident profile reveals a deliberate shift in operational philosophy. DPRK-linked groups accounted for only 12 percent of the total number of hacks, yet captured 60 percent of total stolen value. CertiK describes the approach as one of “precision and scale”: fewer operations, each surgically aimed at the largest available pools of capital. The pattern abandons the low-yield phishing campaigns of earlier years in favor of multi-stage compromises that take months to engineer.
The Bybit exploit in February 2025 stands as the single largest event. Hackers drained approximately $1.5 billion in a supply-chain attack on a third-party signing provider. CertiK attributes the operation to the TraderTraitor cluster. Onchain analysis tracked the laundering sequence: within one month, about 86 percent of the stolen Ether moved into Bitcoin via mixing services, cross-chain bridges, decentralized exchanges and over-the-counter brokers. The speed and liquidity of the conversion route indicate meticulous pre-planning and access to professional laundering networks.
Physical Infiltration Replaces the Phishing Template
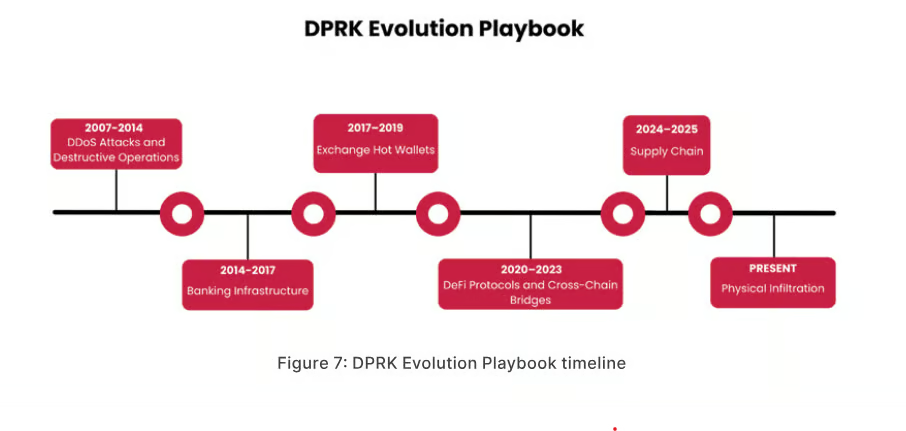
CertiK’s timeline of tactics traces an arc from digital deception to real-world penetration. Social engineering remains the dominant initial attack vector, using fake job offers, investor impersonation and malicious code repositories. The Ronin Bridge exploit in 2022 relied on a spearphishing campaign involving a counterfeit LinkedIn recruiter and a malware-laden PDF. Bybit exemplifies the supply-chain compromise where attackers manipulated a user interface to redirect funds to a malicious address without altering the visible transaction content.
The most recent evolution, documented in the April 2026 Drift Protocol incident, moves the threat into physical space. A group drained approximately $285 million from a Solana-based platform after a six-month operation that included conference attendance, personal relationship-building and governance manipulation.
Jonathan Riss, blockchain intelligence analyst at CertiK, describes DPRK-linked operations as blends of intelligence tradecraft and technical exploitation.
North Korean IT workers and intermediaries secure trusted roles inside Western crypto and fintech firms under false identities, a vector that bypasses perimeter-based security entirely.
The infiltration of legitimate workplaces allows attackers to map internal systems, influence protocol decisions and position themselves for a single catastrophic extraction. Governance tokens, multi-signature schemes and core developer access become targets because compromising a few individuals can unlock an entire treasury. The Drift Protocol case demonstrates how a sustained physical presence can yield a payout matching or exceeding the largest remote exploits.
CertiK’s report frames the cumulative theft as an industrialized state revenue stream. The $2.06 billion captured in 2025 represents a material fraction of North Korea’s external income, given that sanctions restrict most conventional export channels.
The regime has structured specialized units, laundering pipelines and recruitment programs that transform stolen crypto into foreign exchange, components and technology for weapons systems. The cycle does not rely on a single exploit; it operates as a continuous production line that absorbs security improvements in one sector and redirects effort toward softer targets.
The macro backdrop amplifies the threat
With global oil prices elevated by the Strait of Hormuz disruption, commodity costs straining import-reliant economies and military expenditure rising, North Korea faces intensified demand for hard currency precisely when the crypto space holds trillions in onchain value. The concentration of funds in cross-chain bridges, decentralized finance protocols and large exchange hot wallets creates a target surface that even sophisticated perimeter defenses struggle to protect against insider threats.
The rapid conversion of ETH to BTC in the Bybit case shows that mixing services and cross-chain bridges continue operating despite sanctions designations. Over-the-counter brokers absorb large volumes without triggering exchange-based compliance alarms. The combination of technical obfuscation and physical-world banking relationships creates a settlement layer resilient to blacklisting, largely because it distributes risk across jurisdictions with uneven enforcement capacity.
Market participants now price the DPRK threat into exchange risk premiums. The Bybit incident did not cause a systemic collapse, but it demonstrated that a single compromise can erase an entire quarter’s protocol revenue. Exchanges and DeFi platforms face mounting pressure to harden contractor verification, monitor insider activity and adopt multi-party computation for transaction signing.
CertiK’s findings drive home a grim feedback loop: the more value the digital asset industry accumulates, the greater the incentive for state-backed adversaries to treat it as an extractable resource. The playbook that began with hot wallet theft now encompasses supply-chain manipulation, identity fraud and on-the-ground cultivation of insiders.


